In the tech world, so many different devices are used to create modern networks that it is difficult to keep track unless you have some kind of vested interest. Various servers, supporting devices, workstations, switches and other things, work harmoniously to deliver a great experience to the end user.
A few kinds of devices are specifically used for security in a networked environment. Most are familiar with a firewall and the underlying concept of operation it provides such as restricting access to certain resources from unwanted entities. Another less commonly known device that handles somewhat similar tasks is called a Session Border Controller (SBC). This device supplements regular firewalls and provides much greater control for an architecture that is using Voice over IP (VoIP).
In this deep dive article we will take a look at what an SBC is, why you might need one and which products are currently popular in the market today.

What is a Session Border Controller (SBC)?
Like a switch or a firewall, an SBC has specific routing functions to manage traffic on a busy network. In the simplest sense, the device or application manages the Quality of Service (QoS) for VoIP calls. Other functions present include the ability to manage threats, such as attacks on the network, as well as provide an additional authentication mechanism for voice or media packets.
These devices or applications improve a network infrastructure where a VoIP implementation is present. Several supplemental benefits include:
- Enhanced security
- Better control of traffic
- Improved media processing
- More interoperability with other systems
Many see this device as a kind of a firewall appliance for a network. In some ways, these devices overlap but the SBC is geared specifically toward handling VoIP transmissions, meaning SIP and other communication-specific protocols such as Inter Asterisk eXchange (IAX.)
Why use an SBC?
This is a question frequently asked by many business decision makers, including IT professionals. Commonly, professionals in technology inexperienced with VoIP on a large scale believe other networking devices such as firewall appliances, switches and routers, have the capability to fully support a VoIP implementation. While this is an understandable notion, there are specific features of an SBC that greatly improve the health of a network.
Although these devices are most commonly integrated on the carrier's network, implementing a properly configured device in a businesses network can help resolve a variety of issues such as the traversal of intermediate systems ALGs (Application Layer Gateways) between your network and a provider. Another benefit comes from the fact that companies providing SIP services generally use these devices to control QoS issues, among others, on their end. Having one on the service end further enhances the interconnection between these networks.
Typically, most firewalls whether Cisco, SonicWall (now Dell) or some SECaaS (SECurity as a Service) solution, have the ability to stop traffic or allow authenticated connections to access certain network resources. There are often problems with the transmission of certain services like VoIP where ports are opened for traffic (typically 5060 and 5061 for SIP) and the ALG for SIP needs to be turned off. This presents a security issue as hackers look for these pinholes to exploit a network.
Difference between a Session Border Controller and a Firewall
A firewall either accepts or denies access to a network based on stateful packet inspection and filtering of layers 3 and 4 of the OSI (Open Systems Interconnection) stack. In comparison, an SBC can inspect traffic up to and including layer 7 which allows for dynamic setup and teardown for real-time communications. Since the Session Initiation Protocol (SIP) works at layer 7, using an SBC allows for a more secure environment, as opposed to just leaving SIP ports permanently open on a Firewall. This ability to initiate, respond to or terminate a SIP session means an SBC can provide a high level of security for SIP enabled traffic, while a firewall is much less effective.
A look at an SBC in a network
An SBC usually sits between the firewall and IP PBX in a business network. Data is first greeted by the firewall then passed to the SBC where the information is appropriately transposed and sent to the PBX. Here, the device interprets the information, relaying signals between these endpoints.
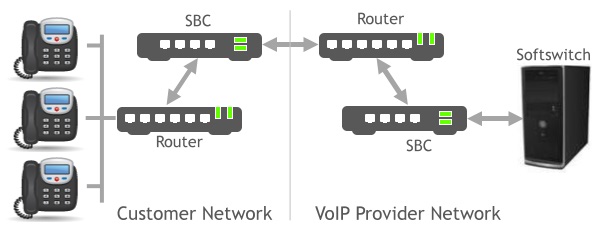
Figure 1: SBC in a network
In certain setup scenarios, implementing such a device or comparable application is critical. Yet in others, companies can get away with proper and secure configuration of security devices and VoIP endpoints.
When is it necessary to deploy an SBC?
Generally speaking, the larger the environment of the VoIP deployment, the greater the necessity for implementation of an SBC device or comparable software. It is especially necessary when a network is so large, that the only feasible way to keep track of devices is with heavy documentation and some kind of monitoring solution.
When making decisions on behalf of a networked environment, a few questions should come into play:
- How well does our network handle traffic to begin with?
This is an important question in any deployment situation. The manner in which a network handles traffic is important to analyze such that good decisions are made on behalf of all network traffic. - Is our setup secure?
Many times, a decision maker with a business perspective sees a setup as secure because they need to put in a password at a couple of different points, like when logging into a workstation and entering a password to login to a virtual machine. Administrators hate hearing users complain and users hate typing extra characters. Unfortunately for both, the more security layers, the less chance of a breach. - What is the quality of your Network?
Perhaps your company has not yet implemented an Internet-based voice solution or is switching providers. Before signing up or building your own service, a granular level of analysis of a network is necessary. If it was bad before, it may be just as bad or worse with VoIP, no matter what a sales representative claims. - Are changes easy to make with a current setup?
Certain systems are notoriously difficult to alter or scale. Some software simply lacks the ability to pull in critical data like an Active Directory or other user databases via LDAP (Lightweight Directory Access Protocol), which makes dealing with some VoIP systems (especially in large environments) a gruesome task. No experienced IT professional truly wants to sit around and create user profiles when an account and groups for users already exists.
The larger the environment, the more moving pieces there are, the greater the involvement in making these pieces move harmoniously. Sometimes the reason these pieces do not move like the gears in a well-oiled machine is because of large staff shifts or a change in an outsourced staffing. In these situations, it is common that certain details pertaining to the setup or operation of the network are not relayed to a new team. Other times, an experienced team is pitted against aging infrastructure and unattractive budgets.
With either situation, a network may run like a neglected vehicle, while it goes from point A to point B with little effort, some level of maintenance would make the process much more efficient. The wisest choice is always making sure connections are secure and programming is solid. However, aging is a continual process and having an SBC in place will help identify and correct certain weak points.
In respect to security, a network breach can mean anything from a bit of snooping from an unauthorized individual up to theft of valuable intellectual property. Consider too, if VoIP is in place, an intruder can make calls on a company�s tab meaning anywhere from a few extra dollars on the bill to the hundreds of thousands. If monitoring is already a neglected process or alerts are not greeted with urgency, an SBC can help prevent very costly issues from misuse.
Poor quality stems from a variety of faults. Errors with equipment, poor connections, too little bandwidth, poor programming, et al, all work together producing problems of varying severity. A solid network infrastructure and adequate bandwidth from a provider are undoubtedly the most crucial component for solid VoIP service. Adding an SBC will assist with the management of traffic and ultimately, the cooperation of all components, making any setup better from a small degree to having a major impact.
Many, but not all, VoIP solutions have the ability to pull in user information from databases such as Active Directory. This makes administering said systems much easier and more cooperative with an SBC. If this is not a feature of a VoIP solution, the SBC can help limit usage with another layer of control integrated with a company directory.
Situations where an SBC may not be required
In smaller environments, with a low number of users, an SBC is not always necessary. Small businesses using one system with a single tenant (i.e. themselves) and a handful of users typically do not need to invest in a device or provision a software solution. Smaller providers of hosted services where VoIP is one of the available products do not necessarily need the capabilities of an SBC. With that said, it should be considered as the business grows, especially should this service become a staple.
An environment where physical or virtual servers and workstations are not a mystery to an admin is likely manageable with tools usually provisioned on a good network. Managed switches, monitored uninterruptable power supplies, a powerful, well-configured firewall and a monitoring service generally do the trick. When these elements are properly utilized, extra management utilities may actually prove to be a burden.
With that said, devices and applications of various price points are available to meet the needs and budget of smaller businesses. Companies with few users likely use a few Microsoft based platforms to handle most computing needs where these machines are likely tied into a mostly secure authentication process. If good practices are applied to such an environment and enough network resources are available to handle traffic, an SBC is most likely an unneeded expense.
Current SBCs on the market
Both physical devices and software applications are available for purchase to handle management of voice and other media traffic on a network. We will look at a few of the more popular brands and software available today.
Physical Devices
- Oracle Acme Packet Series
Oracle is named by Forbes as one of the most valuable brands in the world. A leader in enterprise computing over the decades because of its developments in various areas of computing, the company today caters to the cloud computing market while furnishing systems and tools for interoperability. The company offers several Session Border Controllers for everything from the smallest business up to mega corporations with 80,000 concurrent sessions. Higher-end systems are designed to meet rigorous security standards, normalize data streams, cost management controls and perform many others. Very large corporations should look no further than the top of line Oracle products as these feature rich devices currently deliver the best performance on the market.

Figure 2: Oracle Acme Packet 6000 Series
- Sangoma Vega Series and NetBorder Carrier
The Canadian-based company Sangoma, originally founded in 1984, has focused on Internet communication since before the World Wide Web came into existence. They build equipment for VoIP services and recently acquired one of the most widely recognized open source PBXs, FreePBX. Its devices are designed to handle very high concurrent sessions with effective routing throughout a secure environment. One of the biggest selling points lies in the heavy focus in catering to Microsoft Lync. Those relying heavily on this solution should consider using one of the various SBC devices offered by Sangoma.

Figure 3: Sangoma NetBorder Carrier SBC
- Sonus SBC
Originally formed in 1997, Sonus is dedicated to providing well-constructed hardware for businesses utilizing VoIP. They focus on physical hardware, namely SBC devices, for improving the integrity of Internet communications. Like the other devices previously mentioned, the Sonus brand is designed to safely handle a large quantity of calls with network safety in mind. They take pride in the ability to provide high availability with a failover mechanism that connects to the PTSN for critical times during an entire network outage.

Figure 4: Sonus SBC 2000
Open-Source Software Session Border Controllers
Several free and open source solutions are available to handle SBC processes and work the same as hardware devices except they are available as software deployable to a physical host or VM (Virtual Machine). We will briefly look at a few of the better options on the market.
- FreeSwitch
Since the founders of this company broke away from the Asterisk project, they maintained focus on the development of a great PBX platform that manifested as FreeSWITCH. While doing so, they managed to build in the capability to provide SBC functions within the platform modules. The two main products on the market, sipXcom and FusionPBX, have built in SBC features. Although not as robust as other solutions, either can be used to provide pure SBC functions without necessarily functioning as a PBX.

Figure 5: FreeSWITCH
- Kamailio
This is a project that originally started under a German company known as Fraunhofer Society in 2001 that later transformed into a system called OpenSER when a few of the developers decided to create an open solution. Today, the project known as Kamailio is the successor which builds on the former project. The application is packaged as a distribution that sits on top of either a Debian or Ubuntu operating system. High-end functions are included with the system such as multi-domain support for businesses providing service to multiple companies, advanced networking features like load balancing and various asynchronous processing capabilities, WebRTC support, a plethora of security features among many others.

Figure 6: Kamilio
- openSIPS
Though this project does not publicly brandish much of its background, since 2008, it has become a respected solution as a SIP server and SBC. Like other systems, it enhances end-to-end support for VoIP services using SIP and other media transmissions. Similar to other systems, it helps manage the granular details of a network where VoIP is utilized. It features a custom scripting language and fortunately, the website features a good deal of documentation in addition to offering occasional workshops for training. Recently, new features have been implemented that include a broader scope of transport protocol support and fraud detection.

Figure 7: openSIPS
Final Thoughts
The SBC is a valuable and often necessary addition to a VoIP deployment. Administrators can enhance the flow of traffic and improve security with a multitude of features included in most systems today. For mid-size businesses through large corporations, implementing one of these devices is generally crucial.
With that said, not every network using real time communication systems require an SBC. Small companies with few network connections do not require the added expense and additional layer in most cases.
When endpoints become impossible to memorize or a network is constantly scaling outward or upward, it is time to strongly consider a Session Border Controller. Free, open source solutions are available which may be a good start for smaller budgets. If the budget can handle a more established brand, reputable, physical devices are likely a better option as support is usually available whether included or at extra cost.